In this tutorial series I'm going to walk you through the damn vulnerable web application (DVWA) which is damn vulnerable. Its main goal according to the creators is "to aid security professionals to test thier skills and tools in a legal environment, help web developers better understand the process of securing web applications and to aid both students & teachers to learn about web application security in a controlled class room environment."
I am going to install DVWA in docker so the prerequisite for this tutorial will be an installation of docker (Docker is not the only way to install DVWA but if you have docker already installed then it may be the easiest way to install DVWA).
To install DVWA in docker run your docker deamon if it's not running already and open a terminal or powershell and type:
docker rum --rm -it -p 8080:80 vulnerables/web-dvwa
It will take some time to pull the image from docker hub depending on your internet speed and after it is complete it will start the dvwa application. In the command we have mapped the image instance's port 80 to our hosts port 8080 so we should be able to access the web application from our host at http://localhost:8080
Now open your favorite web browser and go to http://localhost:8080
You should be prompted with a login screen like this:
login with these creds:
username: admin
password: password
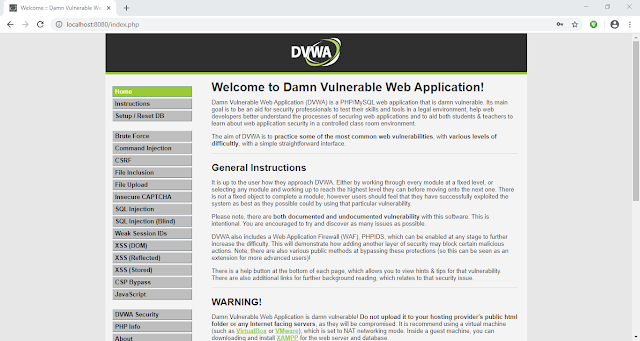
After login you'll see a database setup page since this is our first run. Click on Create / Reset Database button at the bottom. It will setup database and redirect you to login page. Now login again and you'll see a welcome page.
Now click on DVWA Security link at the bottom of the page navigation and make sure the security level is set to Low. If it is not click on the dropdown, select Low and then click submit.
Now our setup is complete, so lets try a simple SQL attack to get a taste of whats about to come.
Click on SQL Injection in navigation menu.
You'll be presented with a small form which accepts User ID.
Enter a single quote (') in the User ID input field and click Submit.
You'll see an SQL error like this:
From the error message we can determine that the server has a MariaDB database and we can see the point of injection.
Since there are many quotes we are not able to determine the exact location of our injection. Lets add some text after our single quote to see exactly where our injection point is.
Now I am going to enter 'khan in the User ID field and click Submit.
Now we can see exactly where the point of injection is. Determining the point of injection is very important for a successful SQL injection and is sometimes very hard too, though it might not be that much useful here in this exercise.
Now lets try the very basic SQL Injection attack.
In the User ID field enter ' or 1=1-- - and click Submit.
We will explain what is going on here in the next article.
References:-
1. DVWA Official Website: http://www.dvwa.co.uk/
- Hacking Tools For Pc
- Hacker Tools Software
- Growth Hacker Tools
- Hacker Search Tools
- Growth Hacker Tools
- Hacking Tools For Pc
- Tools 4 Hack
- Hack Tools For Ubuntu
- Hacker Tools For Mac
- Pentest Tools Github
- Pentest Recon Tools
- Hacking Tools For Windows 7
- Best Pentesting Tools 2018
- Hacker Tools Hardware
- Install Pentest Tools Ubuntu
- Hacking Tools For Beginners
- Hack Tools Mac
- Install Pentest Tools Ubuntu
- Hacking Tools Download
- Hacker Tools Apk
- Hacking Tools 2020
- Tools Used For Hacking
- Tools Used For Hacking
- Hacker
- Tools For Hacker
- Pentest Tools For Windows
- Hacker Tool Kit
- Hack Tools Github
- Growth Hacker Tools
- Hack Tools For Pc
- Hacking Tools Software
- Hack Tools Pc
- Hacker Search Tools
- Hack Tools For Games
- Hacker Tools
- Pentest Tools Open Source
- Hack Tools Online
- Computer Hacker
- Pentest Tools List
- Hacking Tools For Kali Linux
- Hack Tools For Ubuntu
- Hacking Tools For Mac
- What Are Hacking Tools
- Pentest Tools For Mac
- Pentest Tools For Ubuntu
- Hacking Tools
- Hacker Security Tools
- Hacking Tools Kit
- Hacking Tools Name
- Hacker Security Tools
- Pentest Automation Tools
- Pentest Tools Apk
- Pentest Tools Website
- Pentest Tools Android
- Hacking Tools Online
- Hack Tools For Ubuntu
- Nsa Hack Tools Download
- Pentest Tools Url Fuzzer
- Hacking Tools For Windows 7
- Hack Tools For Games
- Pentest Reporting Tools
- Hacker Tools Mac
- Pentest Tools Github
- Hacker Tool Kit
- Pentest Tools Website Vulnerability
- Pentest Recon Tools
- Hacker Search Tools
- Hack Tools Github
- Hack Tools For Pc
- Hacking Tools Github
- Hack Tools Pc
- Hack Tools
- Pentest Tools Open Source
- Hacker Tools Online
- Hacking Tools Mac
- Hacking Tools 2020
- Github Hacking Tools
- Hacker Tools Linux
- Pentest Automation Tools
- Hacking Tools For Mac
- Hack Apps
- Pentest Tools Review
- Hack Tool Apk No Root
- Pentest Tools Nmap
- Hacker Tools Online
- Hacking Tools For Kali Linux
- Hacker Tool Kit
- Pentest Tools Find Subdomains
- Pentest Reporting Tools
- Pentest Tools Download
- Hackers Toolbox
- Hacker Tools Hardware
- Pentest Tools Android
- Hacking Tools Github
- How To Hack
- Pentest Tools Open Source
- Pentest Tools Online
- Hacking Apps
- What Is Hacking Tools
- Easy Hack Tools
- Pentest Box Tools Download
- Hacker Tools Software
- Hacker Tools List
- Hacking Apps
- Hacker Tools For Windows
- What Is Hacking Tools
- Game Hacking
- Hacker Tools Software
- Hacker Tools 2020
- Hacking Tools Github
- Hack Tools Download
- Hack Tool Apk No Root
- Hack Tools
- What Is Hacking Tools
- Pentest Reporting Tools
- Hacking Tools 2019
- Hacking Tools For Beginners
- Pentest Reporting Tools
- Game Hacking
- Hack Tools For Windows
- Hacker Tools Apk
- Pentest Tools Website
- Hacker Tools Online
- Hack App
- Pentest Tools Windows
- Hacking Tools Free Download
- Pentest Tools For Ubuntu
- Hack Tools
- Hacker Tools For Pc
- Hacker Tools For Windows
- Pentest Tools For Windows
- Hacker Tools 2020
- Hacker Tools Apk
- Pentest Tools Find Subdomains
- Hacking Tools For Mac
- Pentest Tools Website Vulnerability
- Hacker Tools For Pc
- Install Pentest Tools Ubuntu
- Nsa Hacker Tools
- Hacking Apps
- Pentest Tools Free
- Free Pentest Tools For Windows
- Hacker Tools 2020
- Nsa Hacker Tools
- Kik Hack Tools
- Hacking Tools Software
- Hacker Security Tools
- Pentest Tools
- Hacking Tools For Beginners
- Pentest Tools For Ubuntu
- Hacker Tools Mac
- Hack Tools Github
- Growth Hacker Tools
- Nsa Hacker Tools
- Hacker Tools Hardware
- Hacking Tools For Windows Free Download











No comments:
Post a Comment